top of page
Company Insights
See the plethora of company insights on Security, Compliance, Management and Risk.



Balancing Admin Rights & Control – Privilege Access Management
Organizations need to have controls in place in place for the management of accounts with privileged access. Privileged access management...
Ascent Portal Staff
Nov 5, 20212 min read


Identify AND Authenticate Users – A “Must Have” Combination
Identify AND Authenticate users in order to protect your organizations networks. Actions performed on an organization’s networks,...
Ascent Portal Staff
Oct 29, 20212 min read


Why a “One-and-Done” Access Control Policy Won’t Cut It
Unauthorized or inappropriate account access is likely to occur within organizations if ongoing maintenance is not in place for all...
Ascent Portal Staff
Oct 21, 20212 min read


Requirements for a Strong Access Control Program
The lack of an overall strong access control program generates opportunities for the unauthorized access to potentially sensitive data in...
Ascent Portal Staff
Oct 19, 20212 min read

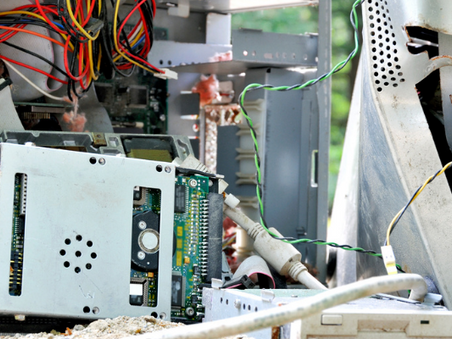
Secure Disposal and Re-Use of Information Assets
Organizations must ensure that the process for the disposal or re-use of equipment is strictly controlled. The improper disposal or...
Ascent Portal Staff
Oct 13, 20212 min read


Media Handling and Protection
Media handling controls should be implemented to protect organizations from the risks associated with the loss of confidentiality,...
Ascent Portal Staff
Oct 8, 20212 min read


Classification, Labeling, and Handling of Information Assets
Information assets, including printed materials, email attachments, or other data, should be classified appropriately to ensure they are...
Ascent Portal Staff
Oct 5, 20212 min read


What Is Acceptable with Asset Usage?
If organizations do not document, communicate, and have personnel agree to acceptable use requirements, personnel may not be limited to...
Ascent Portal Staff
Sep 30, 20212 min read


Know What You’ve Got – IT Asset Inventory
IT Asset inventories help your organization control IT costs, reduce risk, and automate modern IT environments. IT Assets cannot be...
Ascent Portal Staff
Sep 24, 20212 min read


Keep Up Security Awareness Training Until You Get It Right
Your organization should develop, document, and maintain a comprehensive Security Awareness Training Program. If security awareness...
Ascent Portal Staff
Sep 21, 20212 min read
bottom of page
.png)